How it Works
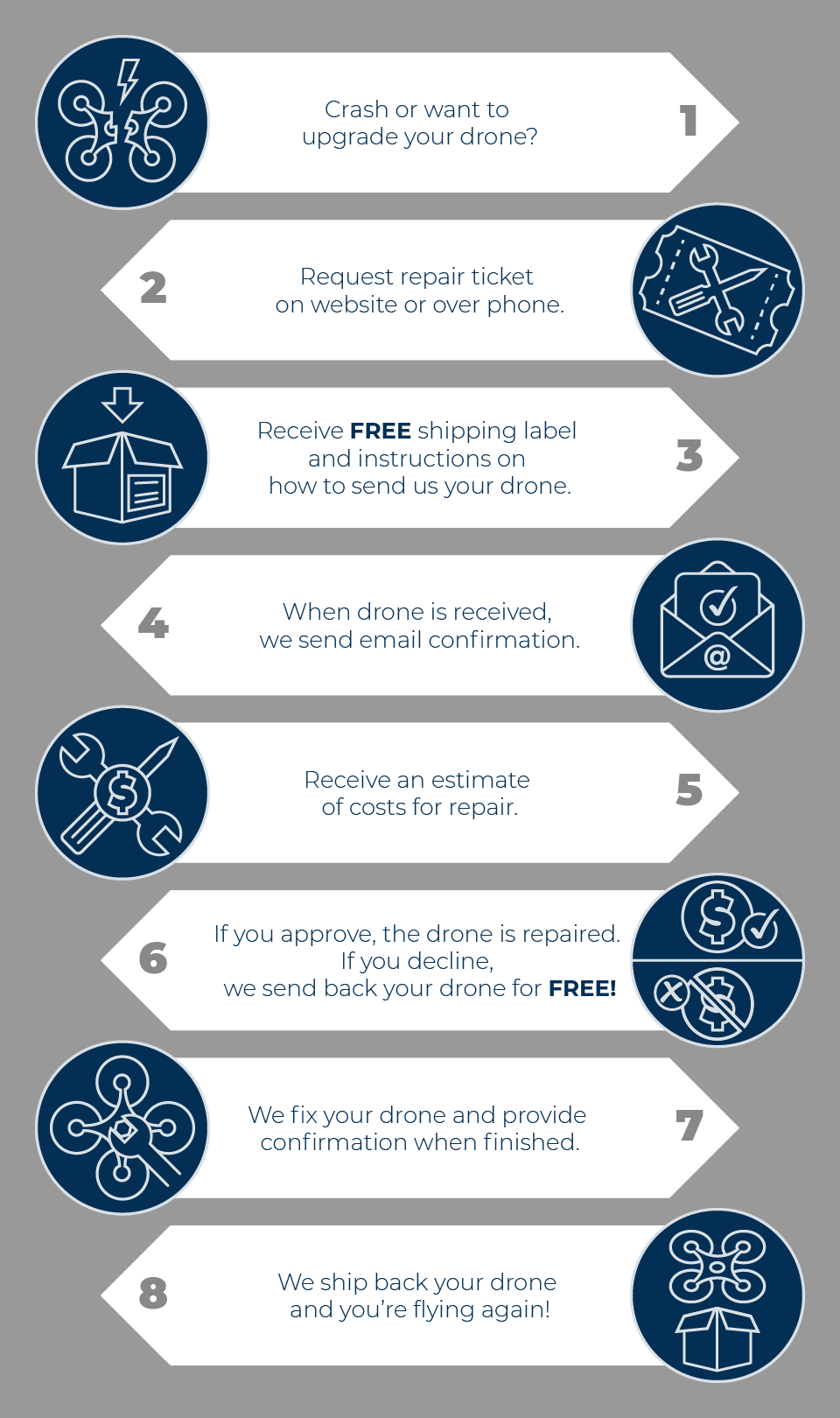
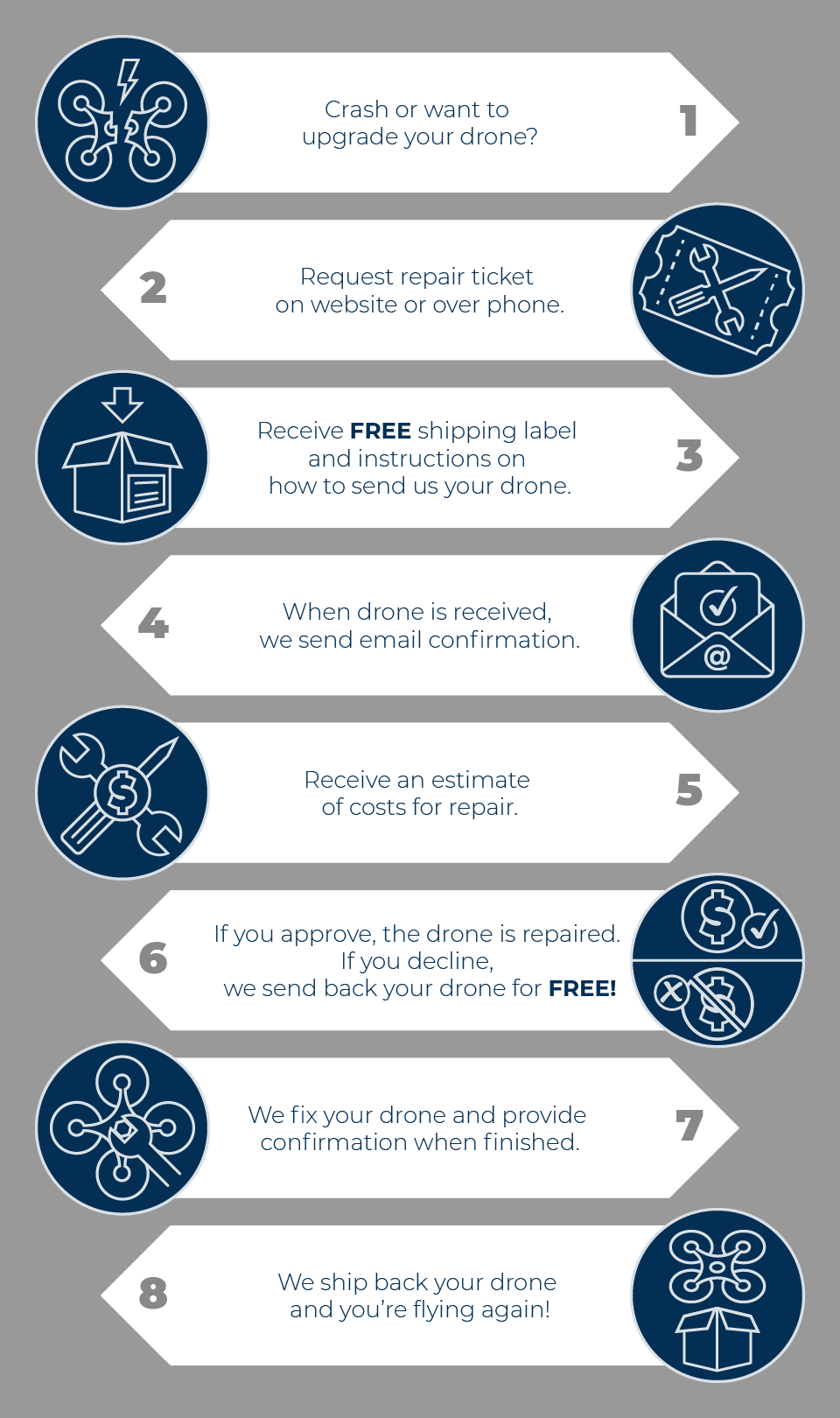
Our technicians here at djidroneservice.com are DJI certified, meaning that they know everything there is to know regarding DJI drone repair. As long as the nature of the damage to your drone is possible to repair, we at djidroneservice.com will happily fix your drone. Whether you have a Mavic, Phantom, or any other type of DJI drone, djidroneservice.com is the place to go for convenient and inexpensive drone repair.
You are not risking any money by sending your damaged drone for inspection, because you only pay if we fix your drone. Djidroneservice.com does not charge inspection fees and shipping is always free. This is our policy even if you do not choose to purchase our repair services. Consider shipping your drone to djidroneservice.com for inspection and repair before you accept the lengthy and expensive repair process you can expect elsewhere.
The Microsoft Windows Remote Procedure Call (RPC) over HTTP 1.0 protocol has been a cornerstone of Windows networking for years, enabling remote communication between systems. However, a vulnerability in this protocol, known as NCACN-HTTP, has been discovered, allowing attackers to exploit and gain unauthorized access to Windows systems. In this article, we will delve into the details of the NCACN-HTTP Microsoft Windows RPC over HTTP 1.0 exploit, its implications, and the measures to mitigate this security threat.
The exploit works by sending a malicious request to the vulnerable system, which is then processed by the RPC over HTTP 1.0 service. The request is designed to overflow a buffer, causing the system to execute malicious code. This code can be used to gain unauthorized access to the system, steal sensitive data, or disrupt system operations. ncacn-http microsoft windows rpc over http 1.0 exploit
To mitigate the NCACN-HTTP exploit, Microsoft has released a patch that addresses the vulnerability. It is essential to apply this patch to all affected systems to prevent exploitation. The Microsoft Windows Remote Procedure Call (RPC) over
The NCACN-HTTP exploit takes advantage of a vulnerability in the RPC over HTTP 1.0 protocol, which allows an attacker to send a specially crafted request to a vulnerable Windows system. This request can trigger a buffer overflow, causing the system to execute arbitrary code, potentially leading to a complete system compromise. The exploit works by sending a malicious request
The NCACN-HTTP Microsoft Windows RPC over HTTP 1.0 exploit is a significant security threat that can have severe consequences for Windows systems. It is essential to understand the vulnerability, its implications, and the measures to mitigate this threat. By applying the patch and implementing additional security measures, organizations can protect their Windows systems from exploitation and maintain the security and integrity of their networks.
Microsoft Windows RPC Over HTTP 1.0 Vulnerability: NCACN-HTTP Exploit**